Blog
Articles about privacy, VPN technology, internet freedom, and security.
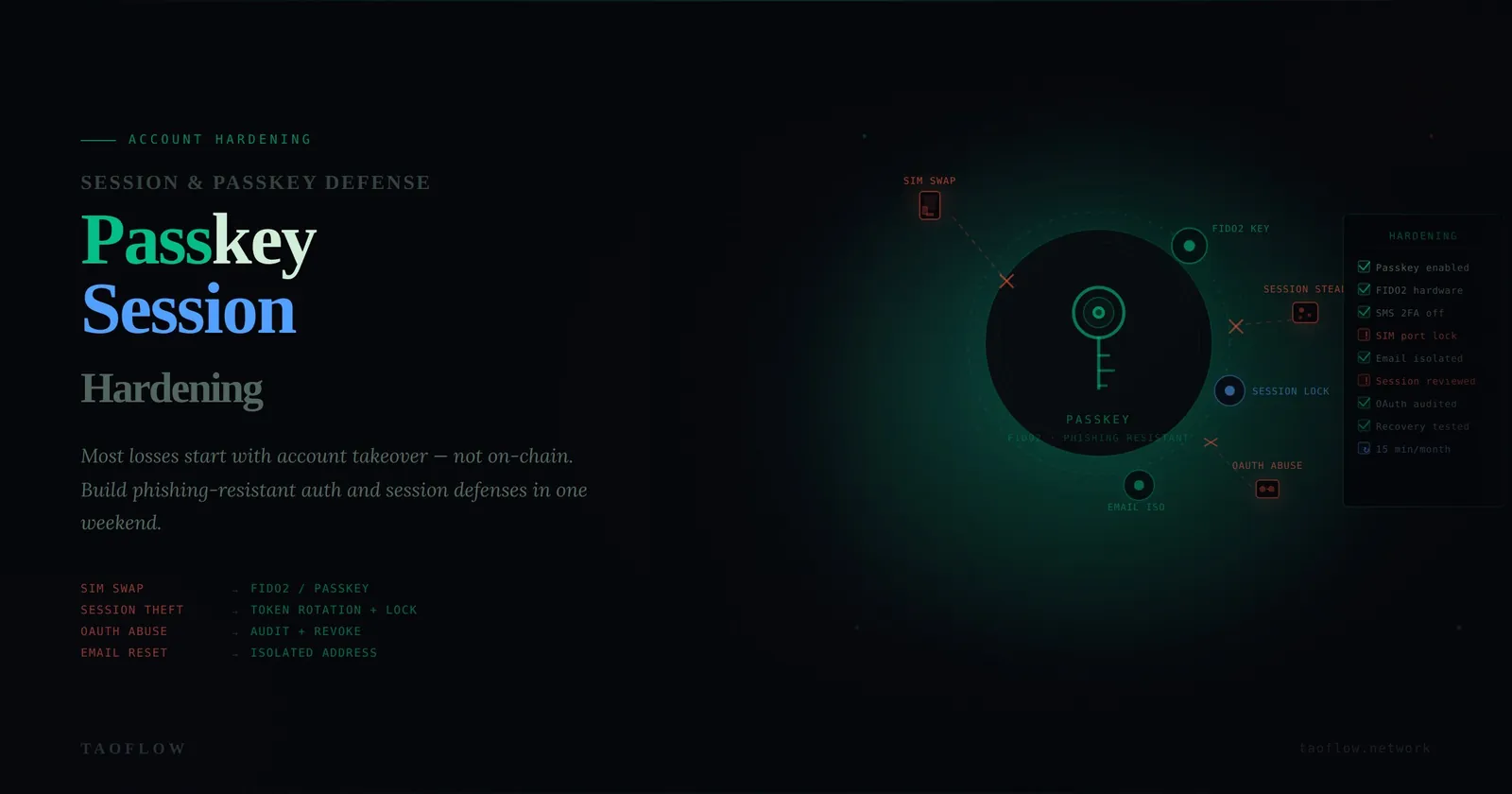
Crypto Account Hardening: A Practical Passkey and Session Defense Checklist
A practical hardening guide for crypto users who want to reduce account takeover risk from SIM swaps, session theft, and OAuth abuse.

Crypto Verification Workflow: How to Catch Address Poisoning Before You Send
A practical verification workflow to prevent address poisoning mistakes in crypto transfers, with checklists you can run in under two minutes.

Crypto Incident Response: A 24-Hour Containment Checklist After a Suspicious Signature
A practical, step-by-step response plan for the first 24 hours after you sign something suspicious—contain damage, preserve evidence, and recover safely.
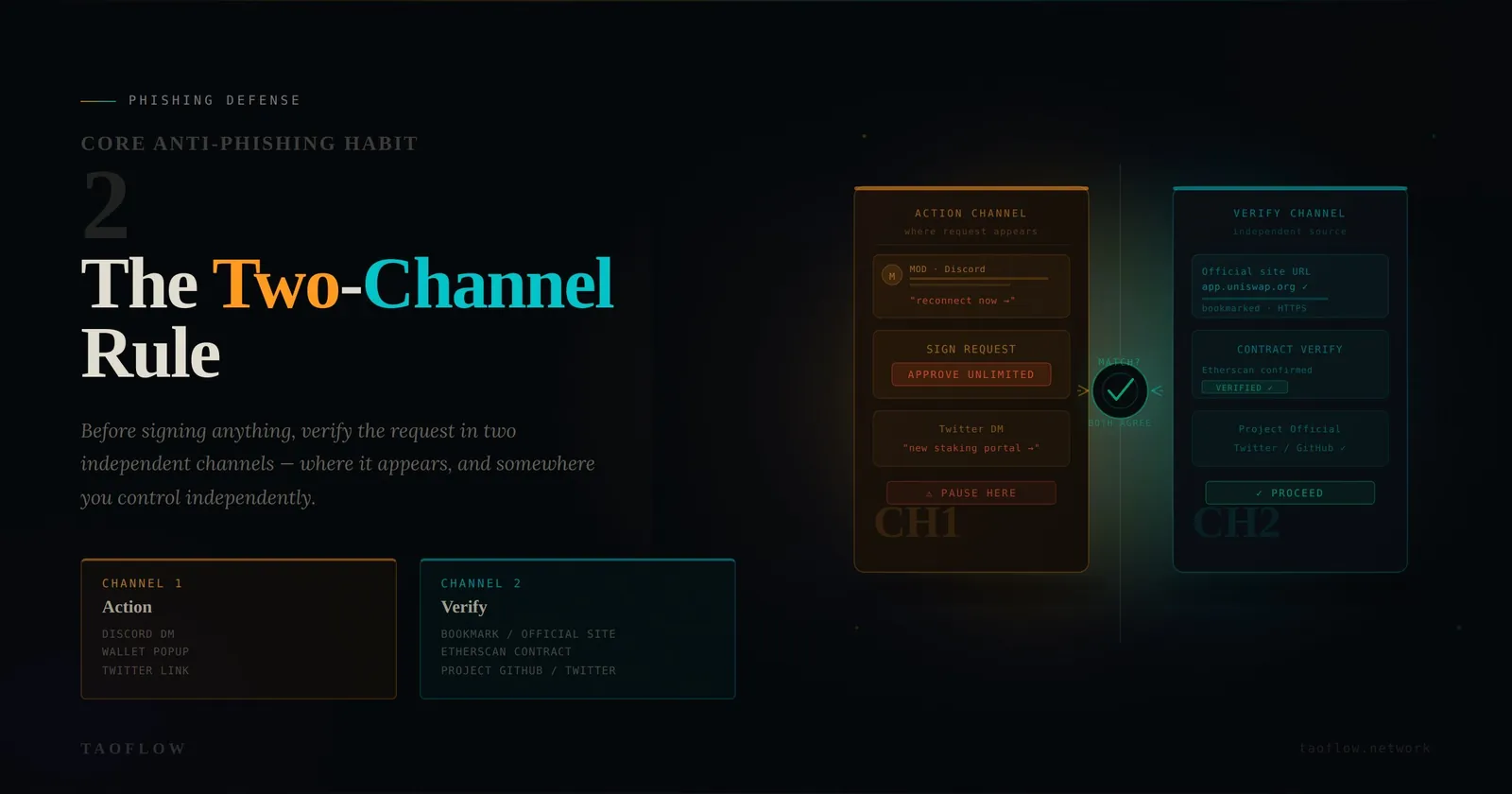
Crypto Phishing Defense: The Two-Channel Rule Before Every Wallet Signature
A practical anti-phishing workflow for crypto users: verify links, contracts, and requests through independent channels before signing anything.
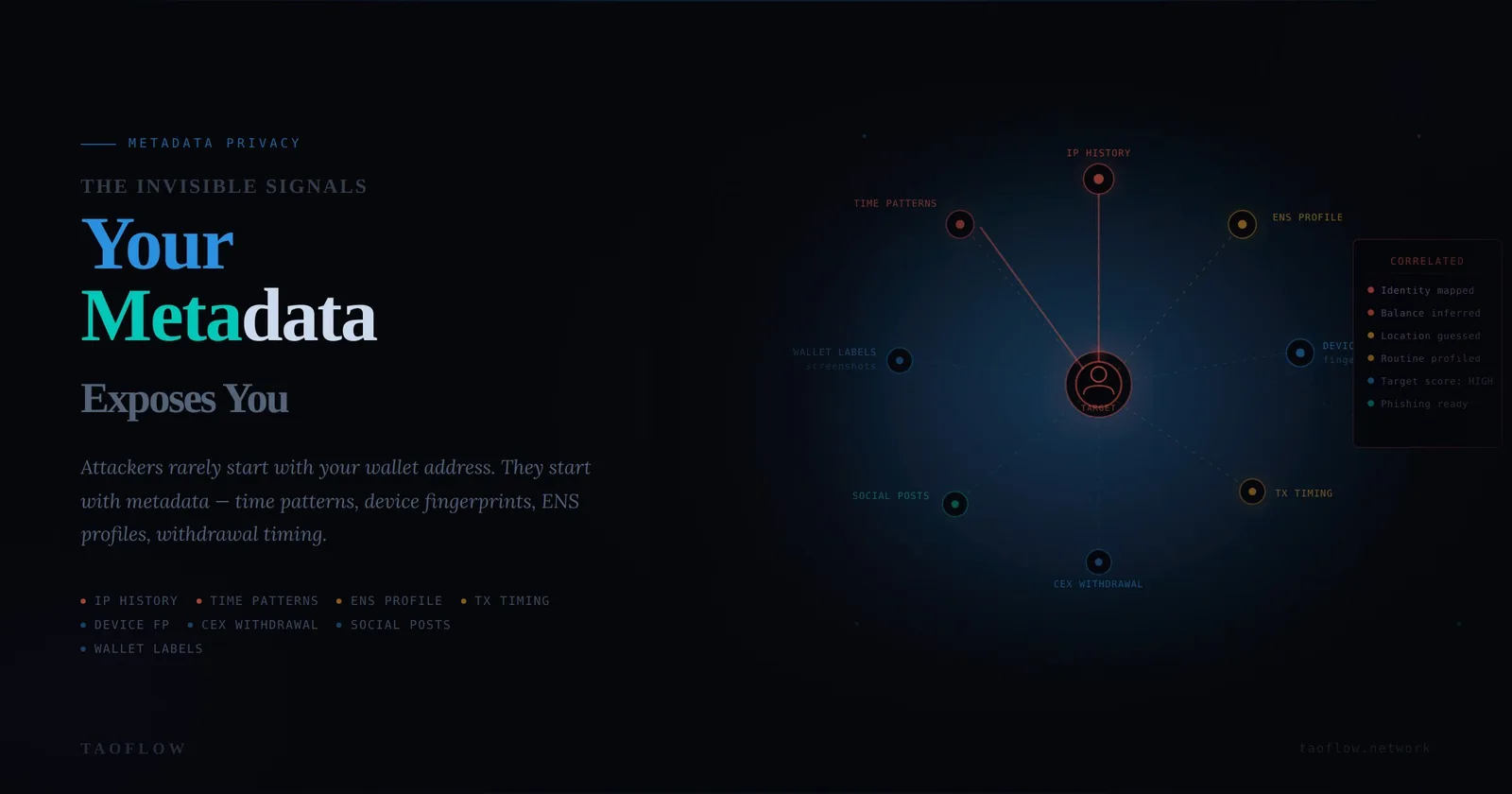
Crypto Metadata Hygiene: A Practical Guide to Reducing Wallet Linkability
A hands-on security guide for crypto users to reduce metadata leaks that connect wallets, identities, devices, and daily behavior.

Crypto Account Hardening Beyond 2FA: A Practical Defense-in-Depth Guide
A practical account hardening playbook for crypto users: stronger MFA, SIM-swap resistance, identity segmentation, and monthly takeover-prevention routines.

Crypto Verification Workflow: A 10-Minute Routine Before You Sign Anything
A practical verification workflow for crypto users to detect phishing, malicious approvals, and address poisoning before signing transactions.

Wallet Recovery Readiness: A Practical Drill Before Your Next Incident
A step-by-step recovery drill for crypto users: validate backups, reduce single points of failure, and rehearse incident response before a real wallet emergency.
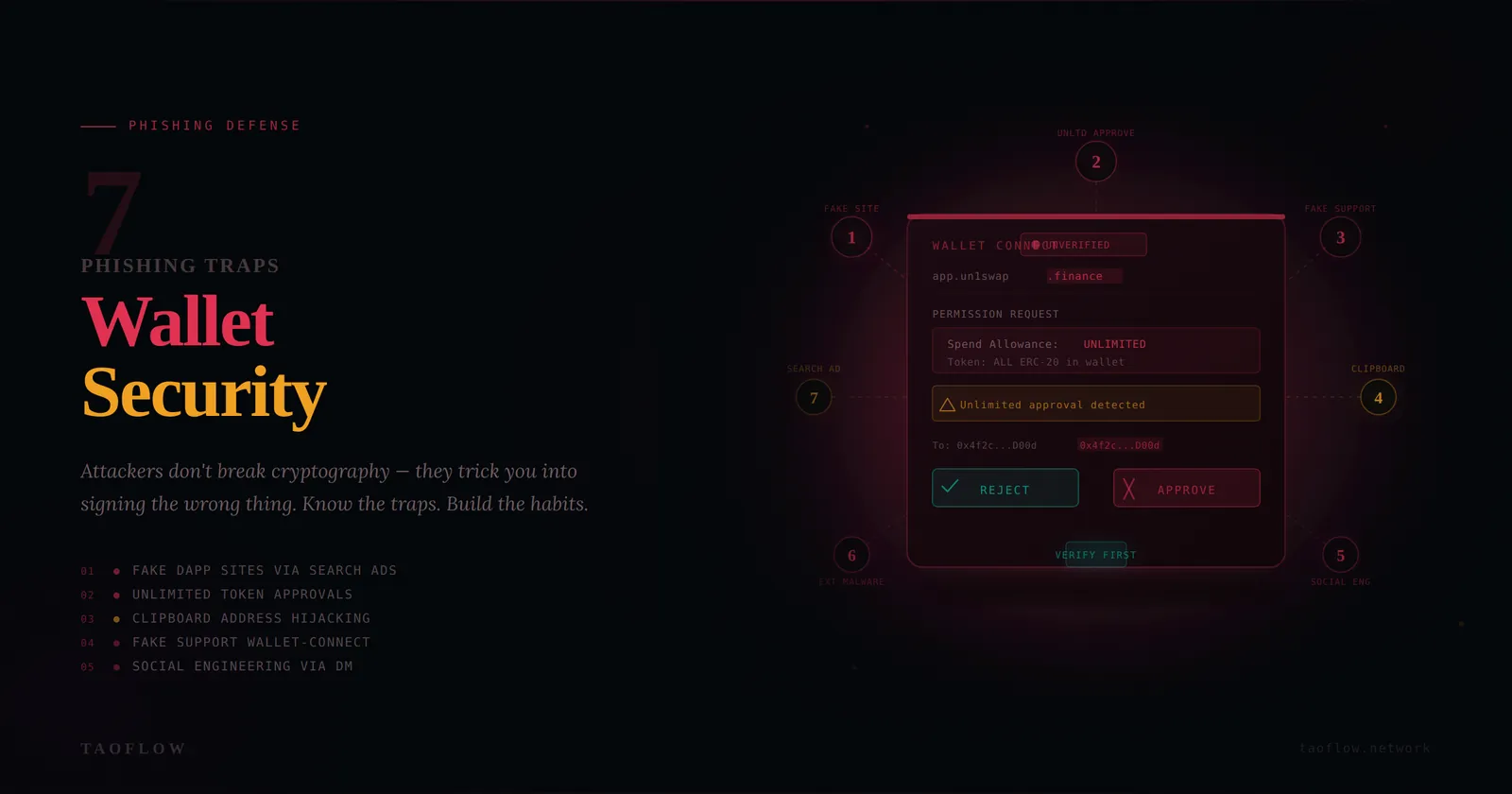
Wallet Security for Crypto Users: 7 Phishing Traps and How to Beat Them
A practical, checklist-first guide to spotting modern wallet phishing traps, verifying transactions safely, and building habits that prevent costly mistakes.

Device OpSec for Crypto Users: A Practical Daily Hardening Checklist
A practical guide to securing your phone and laptop for crypto use, with threat models, quick checks, and incident-response habits you can apply today.

Crypto Metadata Privacy Checklist: Reduce Your On-Chain Linkability Without Advanced Tools
A practical guide to metadata privacy for crypto users: threat model your traces, shrink linkability across wallets and devices, and build daily habits that reduce exposure.
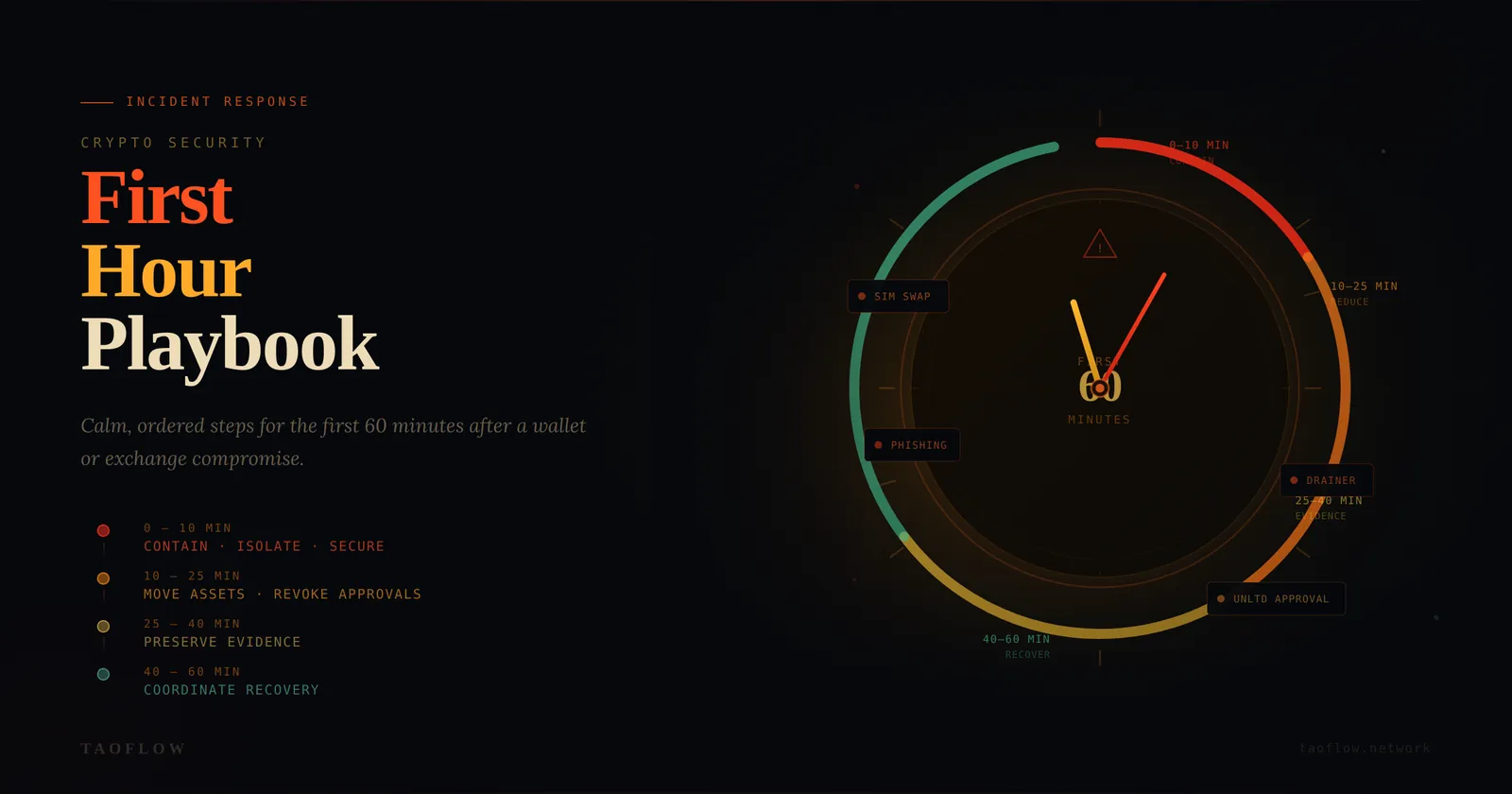
Crypto Incident Response Playbook: The First 60 Minutes After a Wallet Compromise
A practical, step-by-step incident response workflow for crypto users: contain damage, preserve evidence, protect accounts, and recover safely after a wallet compromise.
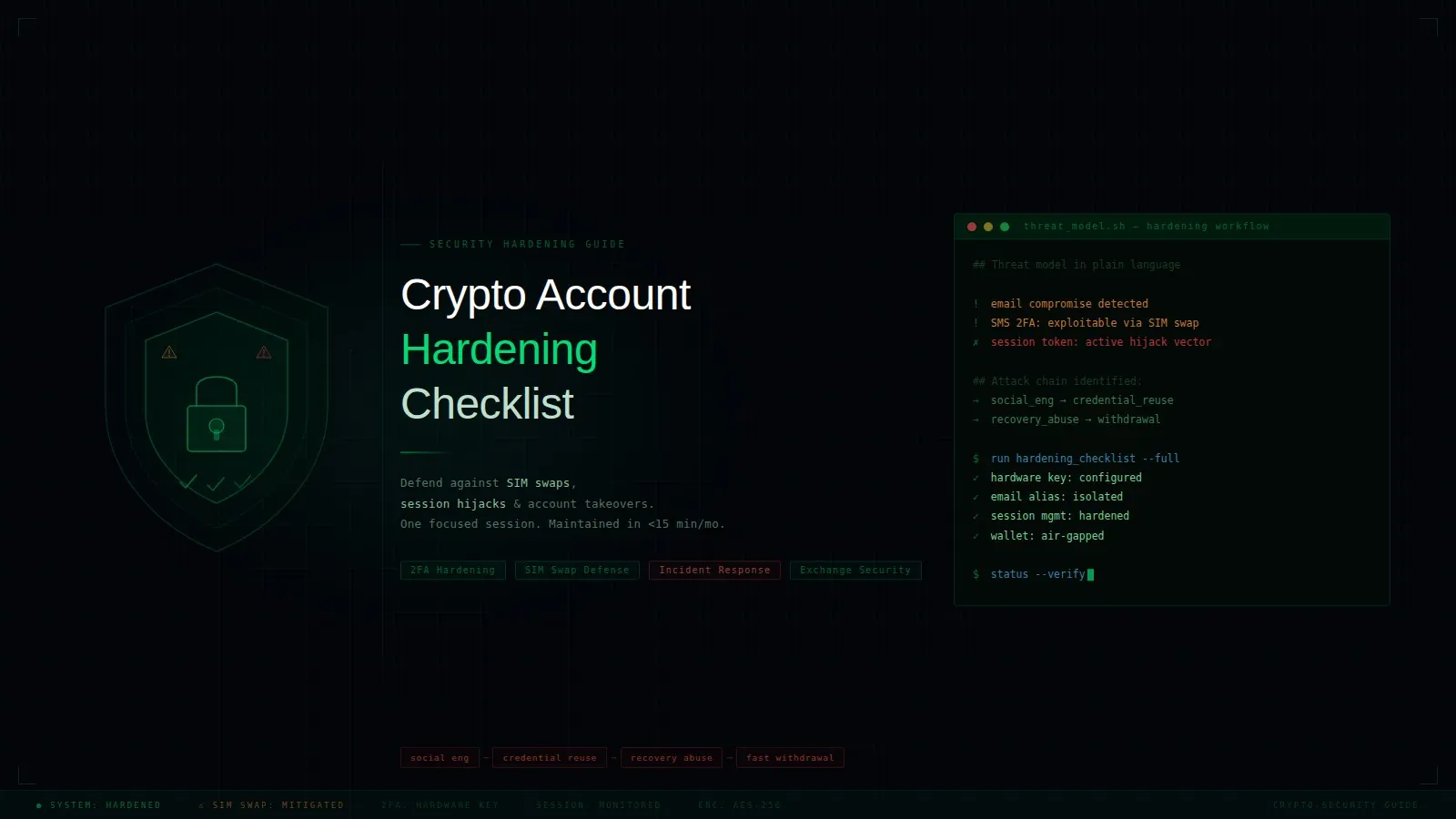
Crypto Account Hardening Checklist: Defend Against SIM Swaps and Session Hijacks
A practical, step-by-step hardening guide for crypto users to reduce account takeover risk across email, exchange, wallet, and mobile recovery paths.

A Crypto Verification Workflow: Stop Phishing Before You Sign
A practical, step-by-step verification routine for crypto users to detect phishing, malicious approvals, and fake urgency before signing any transaction.
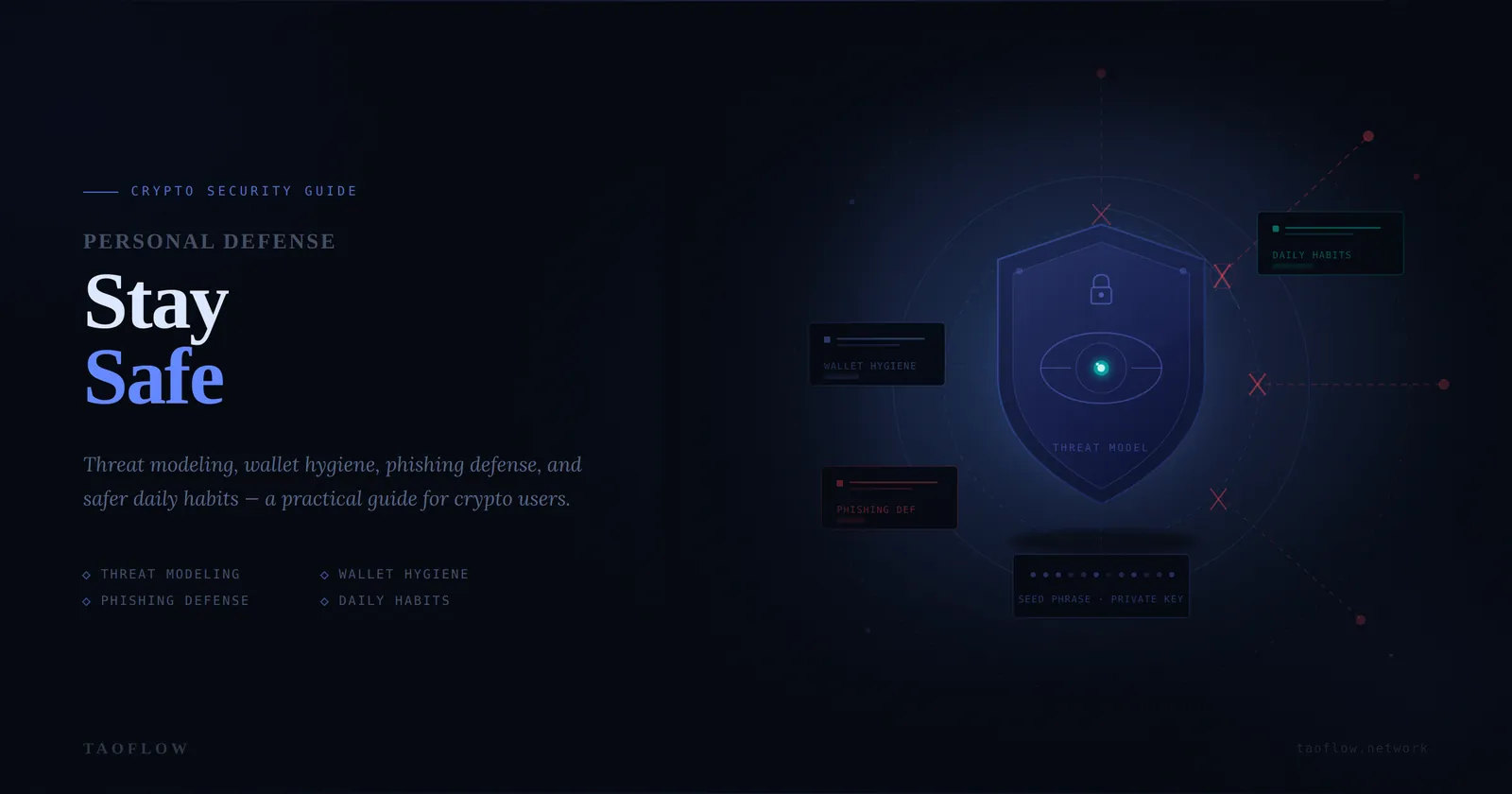
Crypto Privacy Basics: Threat Models and 7 Daily OpSec Habits
A practical, non-promotional guide to personal security and privacy for crypto users: threat modeling, wallet hygiene, phishing defense, and safer daily habits.
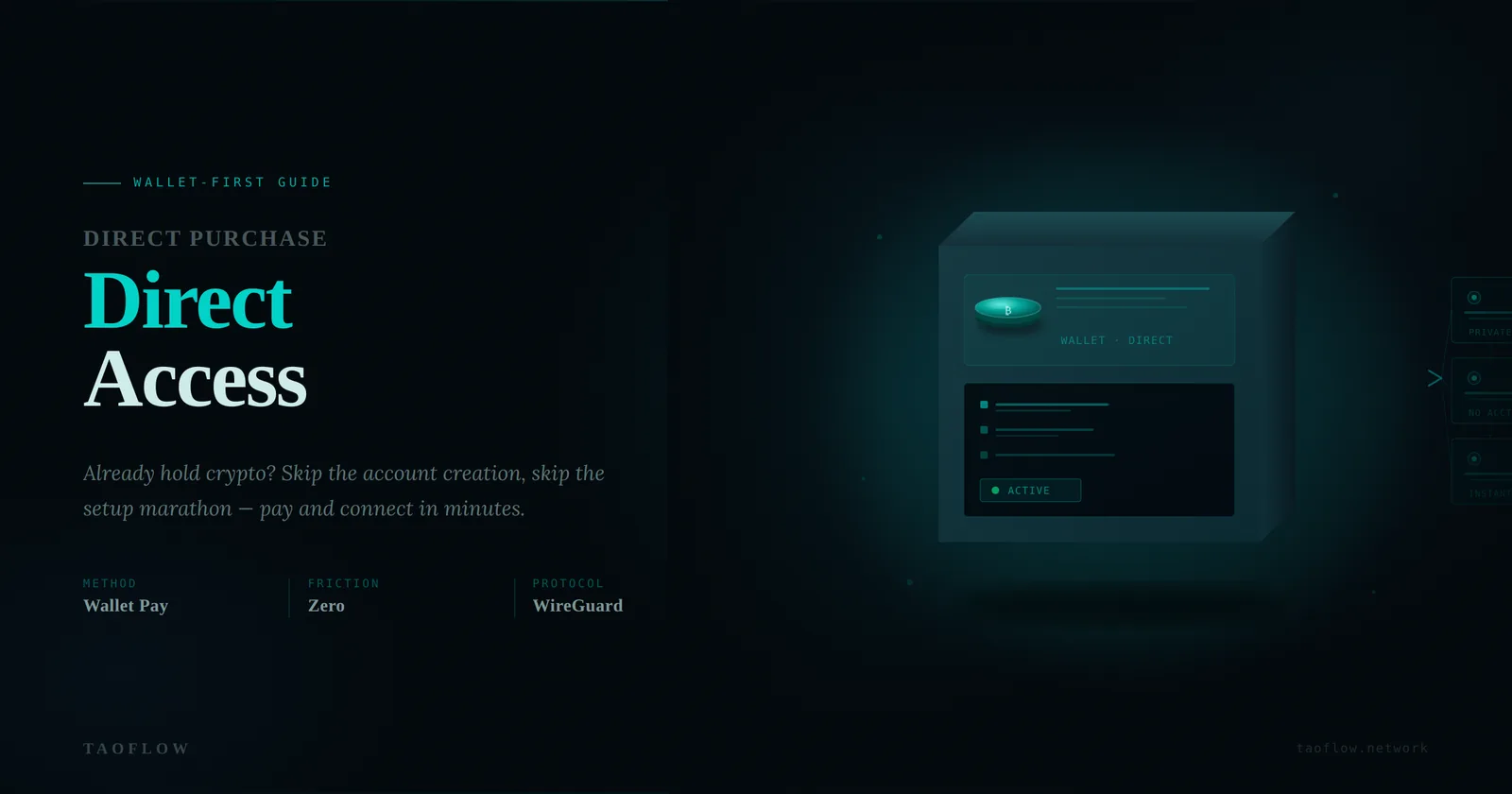
No-Signup VPN for Crypto Wallet Users: A 3-Step Private Access Workflow
A practical, wallet-first guide for people who already use crypto and want private web access fast—no account creation, no setup marathon, just direct purchase and direct use.
Stop Server-Hopping: A Wallet-First Playbook for Private Web Access in 2026
A practical playbook for crypto wallet users who want private, reliable web access without signup friction, app-heavy VPN setup, or endless server-hopping.
Stablecoin Privacy in 2026: How to Access the Open Web Without VPN Setup Friction
Beyond VPN Setup: A Crypto-Native Way to Access the Open Web in 2026
Already using a crypto wallet but tired of VPN setup and account friction? Learn how a no-signup, direct-purchase, direct-use model gives you private web access with context-aware browsing in minutes.
Why TaoFlow Chooses Registration-Free Purchase
In the VPN and privacy-service industry, many platforms require users to register with an email address or phone number before purchase. While this looks standard, it conflicts with a core privacy principle: the more identity data you collect, the higher the risk of leakage and cross-platform correlation.
Why I Created TaoFlow
On today’s internet, access is often treated as something ordinary. Open a browser. Visit a site. Read, learn, communicate. For many people, that feels normal. But the more I thought about it, the more I realized that for many others, it is not normal at all. Some people live in environments where information is limited.